What is a Supply Chain Attack? – ForeNova Technologies
In December 2020, U.S. software developer SolarWinds was exposed as the victim of a major cyber-attack. The threat actor behind the attack installed a backdoor into the software updates of its Orion Platform. The backdoor gave the attacker direct access to the computer networks of 18,000 Orion customers. These include the highest echelons of the U.S. government and some of the world’s largest enterprises.
“I think from a software engineering perspective, it’s probably fair to say that this is the largest and most sophisticated attack the world has ever seen.”
Microsoft President Brad Smith.
The SolarWinds incident is an example of a rapidly growing and dangerous type of cyber-attack known as supply chain attacks.
What are Supply Chain Attacks?
A supply chain attack is a cyber-attack where a threat actor gains illegal access to an organization’s computer network by targeting a third-party supplier or partner with access to the network.
How Supply Chain Attacks Work
Supply chain attacks exploit the trust relationship between an organization and its third parties. Attackers first identify suppliers and partners of a target’s IT infrastructure, such as its software and network devices. The third party is then breached, and the product supplied to the target organization is tampered with. This gives attackers unrestricted access to the target network. The third party serves as an attack vector (point of entry) to breach higher value targets. These are mostly large enterprises and government agencies. Attackers operate inside the target network to stage bigger attacks, such as ransomware attacks, data exfiltration, and cyber espionage.
Types of Supply Chain Attacks:
Software Supply Chain Attacks
In a software supply chain attack, threat actors exploit the software vendors of their targets. This is done by compromising stages of the software development lifecycle. As in the SolarWinds attack, software updates are often targeted. Attackers first gain access to the software’s update server and inject the software update package with malicious code. When the target organization downloads and installs the tainted updates, attackers gain a direct route into the network. The trusted digital signatures of software updates mean that they can easily evade the detection of security tools. The SolarWinds attack is one of the most far-reaching software supply chain attacks in history.

Managed service providers (MSP) are often used as a pivot to launch software supply chain attacks. MSPs are third parties that remotely manage the IT infrastructure and network devices of other organizations. MSPs deploy software and hardware in their customers’ environment, which gives them deep access and visibility of the network. This is what makes MSPs attractive to attackers looking to infiltrate its customers. An example of an attack on MSPs is the Kaseya ransomware attack in 2021.
Hardware Supply Chain Attacks
Hardware supply chain attacks are a less common type of supply chain attack. In a hardware supply chain attack, network device components are tampered with. This makes hardware supply chain attacks difficult to carry out and often involve a state actor. Although hardware-based attacks are rare, the consequences can be severe. Tampered components are extremely hard to detect and can remain hidden for years. For example, network devices may be installed with chips that can copy and send data out of the network. Organizations victim to hardware supply chain attacks can suffer large-scale data breaches and long-term spying.
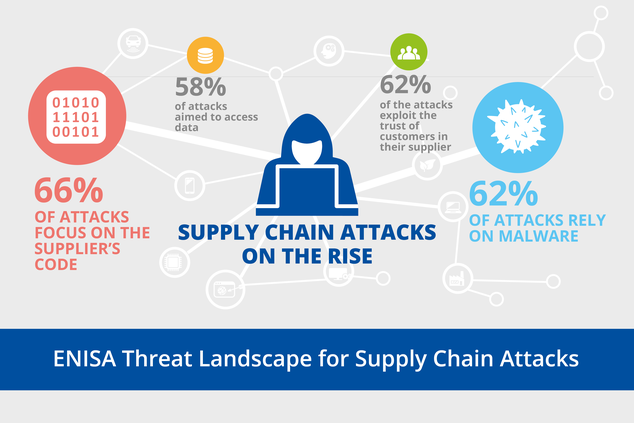
Supply Chain Attacks are on the Rise
Supply chain attacks have become one of the fastest growing cyber threats. They have received widespread attention as a result of high-profile attacks in recent years.
(Infographic from ENISA)
Why are Supply Chain Attacks Growing?
Cyber security technologies have evolved rapidly in recent years in response to advanced adversary tools and techniques. Large enterprises and government agencies, which are the main targets of supply chain attacks, have built multi-layered defense systems. Many have a dedicated IT security team and/or make use of managed security services (MSS). These measures strengthen the security posture of these organizations and make them much harder to penetrate. Attackers would need to develop new tools and techniques and plan new attack strategies. This takes time and money and reduces the reward of an attack.
Smaller third-party suppliers and partners, on the other hand, typically have less advanced cyber security technologies. They may not even have a dedicated security team. This makes third party organizations ideal springboards from which to launch an attack.
Examples of Supply Chain Attacks
Apart from the SolarWinds attack, there have been a number of notable supply chain attacks targeting software and hardware suppliers.
Kaseya Ransomware Attack
In July 2021, IT software developer Kaseya suffered a ransomware supply chain attack. The ransomware group REvil exploited a bug in Kaseya VSA, a remote monitoring and management software popular among MSPs. The flaw allowed the attacker to bypass authentication and execute code on VSA servers. The attack affected roughly 60 direct Kaseya VSA customers and 1,500 downstream customers.
Codecov
In April 2021, US technology company Codecov reported it had suffered a supply chain attack. The hacking group managed to modify the company’s software testing platform, which is used by over 29,000 customers worldwide. This allowed the attackers to steal sensitive information such as source code and secrets from CodeCov’s customers.
NSA Mass Hardware Tampering
In May 2014, the book No Place to Hide shed light on a mass surveillance campaign by the NSA. The book claims that the NSA routinely received or intercepted network devices such as routers and servers, including those of Cisco. The NSA implanted backdoor surveillance tools into the devices before they were shipped to customers worldwide.
Protect Against Supply Chain Attacks Using NDR
The trusted nature of third-party products means that mitigations alone are not enough to prevent attacks. What is needed is a tool that can detect the attacker’s activities once they have infiltrated the network.
The tool in question is Network Detection and Response.
Network Detection and Response (NDR) is a network security technology that analyses network traffic to detect cyber threats. NDR solutions like NovaCommand are what are known as anomaly-based detection tools. These tools use machine learning to build and learn baselines of normal network activity. AI-powered behavioral analytics analyses real-time network traffic and compares results with these baselines. Detected anomalies are correlated with activity across network devices to provide greater context. For supply chain threats, NDR can specifically monitor the supply chain infrastructure like software servers to detect irregular behavior. Credible threats are reported for further investigation and incident response or remediated through automation.
This method of threat detection accurately identifies the highly evasive techniques used by threat actors. These are not picked up by signature-based security tools like anti-virus and anti-malware software.
Endorsement of Anomaly Detection to Protect Against Supply Chain Attacks
CISA recommends that “an organization should identify its critical data and baseline how that data flows between processes or systems. Defenders can deploy analytics, including those based on machine learning/artificial intelligence, to identify subsequent anomalies in data flows, which may be early indicators of a threat actor’s exploitation of a vulnerability.”
How to Respond to a Supply Chain Attack, by Gartner, Inc.
Gartner notes that “Supply chain attacks might leverage multiple attack techniques. Specialized anomaly detection technologies, including endpoint detection and response (EDR), network detection and response (NDR) and user behavior analytics (UBA) can complement the broader scope covered by security analytics on centralized log management/SIEM tools.”